Need penetration testing, forensics, or reverse engineering software or tools for your iPhone? If so, you’ve found the right place, as we’ve compiled a collection of the best resources available to ethical hackers and iOS platform developers. Notable software includes iRET, Cycript, netKillUIbeta, etc. On the other hand, Android has many hacking apps and tools readily available for download. The primary reasons include the security of the iOS platform, the inability to distribute hacking applications through the App Store, and the necessity of jailbreaking the iPhone to install iOS hacking software. Following my discussions on the best Android hacking apps and the best tools for Windows, Linux, and Mac, I will go on to review the best forensic, reverse engineering, and penetration testing tools for iOS and iPhones. Many of them don’t fit the bill of “hacking tools,” but they can come in handy if you’re interested in learning about ethical hacking and working with iOS. The aforementioned hack apps for iOS are provided for educational purposes only. Developers and ethical hackers can use these instruments to ensure the safety of their products.
Hack Apps for iOS | iOS Tools for 2022
iRET – iOS Reverse Engineering Toolkit
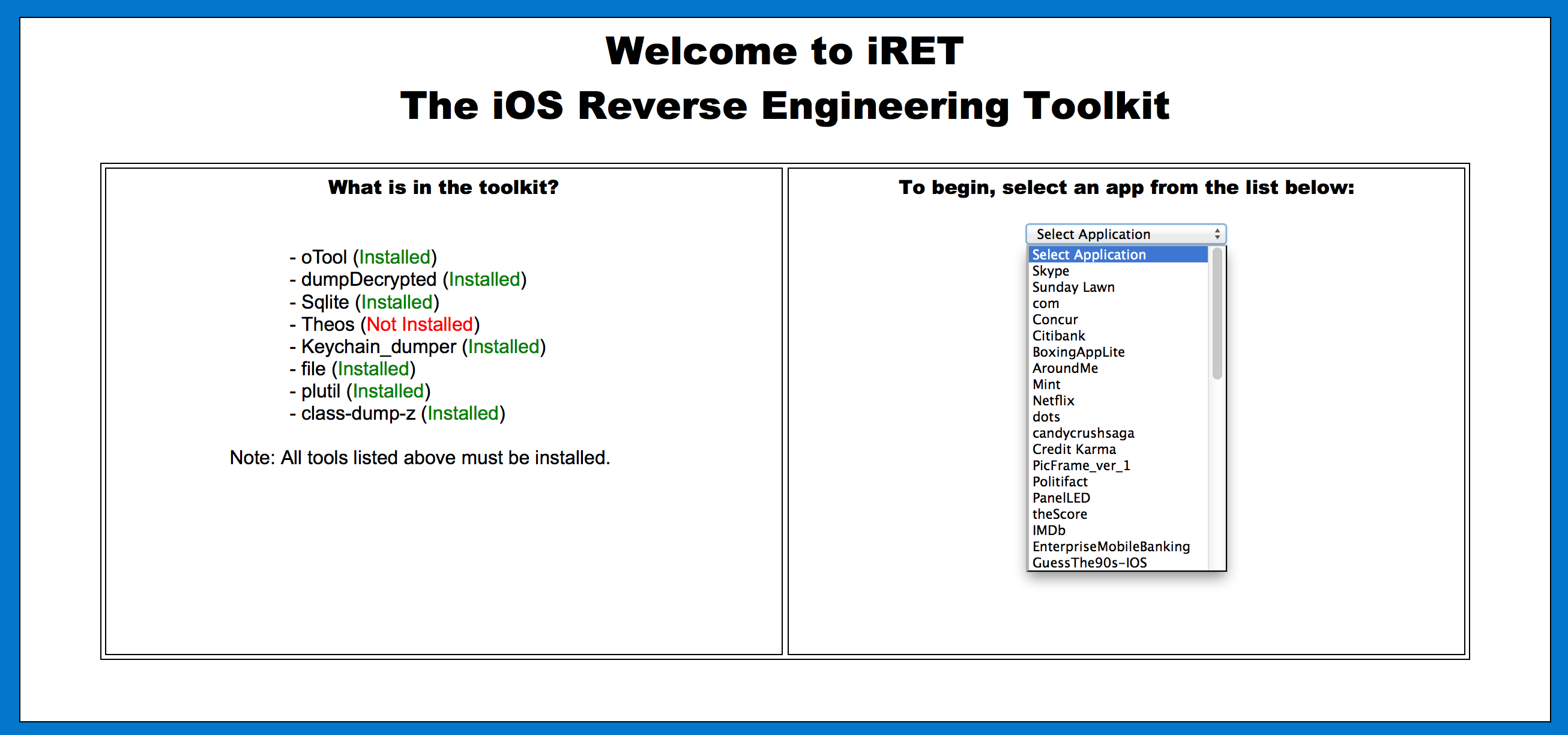
A pen tester’s performance and productivity depend on their ability to do a small set of well-defined, routine tasks. Some examples of these errands include making identical inputs to run different hacking commands on an iPhone. With this problem in mind, Veracode built iRET (iOS Reverse Engineering Toolkit). To use this static analysis tool, you must have Python installed.
Major Features:
- Otool for binary analysis and SQLite for reading database content.
- Perusing log and plist files.
- Use a keychain dumper and customized Theos for diving deeply into a keychain’s inner workings.
netKillUIbeta
Valid hack apps for iOS and Wi-Fi cracking software are hard to come by. However, netKillUIbeta is a tool that aims to prevent idle devices from using network bandwidth, and it performs the same function as WiFiKill for Android.
Install netKillUIbeta and any other prerequisites from the repository at https://extigy.github.io/repo/ on your iOS device. Know that you can trace your malicious actions to your MAC address.
Major Features:
- Do not let unused gadgets eat up your network’s resources.
- WiFi Kill for Android has equivalent features.
iWep Pro
![]()
There are several uses for iWep Pro, a wireless utility app for iOS devices. With it, you can test your router’s security and create a WEP key for your wireless network. This widely-used iPhone exploit is also regularly used to break into wireless networks. It can decipher the password at a specific time, albeit this varies with the type of encryption used.
Major Features:
- Find out if the router has any security flaws.
- Descifrating wireless network passwords.
Myriam iOS Security App

Myriam iOS Security App, developed by security researcher and GitHub user GeoSn0w, is the next app on our list of iPhone hacking applications for 2022. He thought it was the best app to learn iOS hacking with. There are a lot of holes in it that could be explored, experimented with, and used to one’s advantage.
In-App Data Modification, App Activation Bypass, and Jailbreak Detection are a few other challenges available within the app. You can also control the app with UIKit Manipulation to open the web page of your choice.
Major Features:
- Ability to manipulate content in UIKit.
- Several holes that a beginner may easily poke and learn from.
- Detecting a jailbreak, changing app data, and activating apps without permission are all possible.
Burp
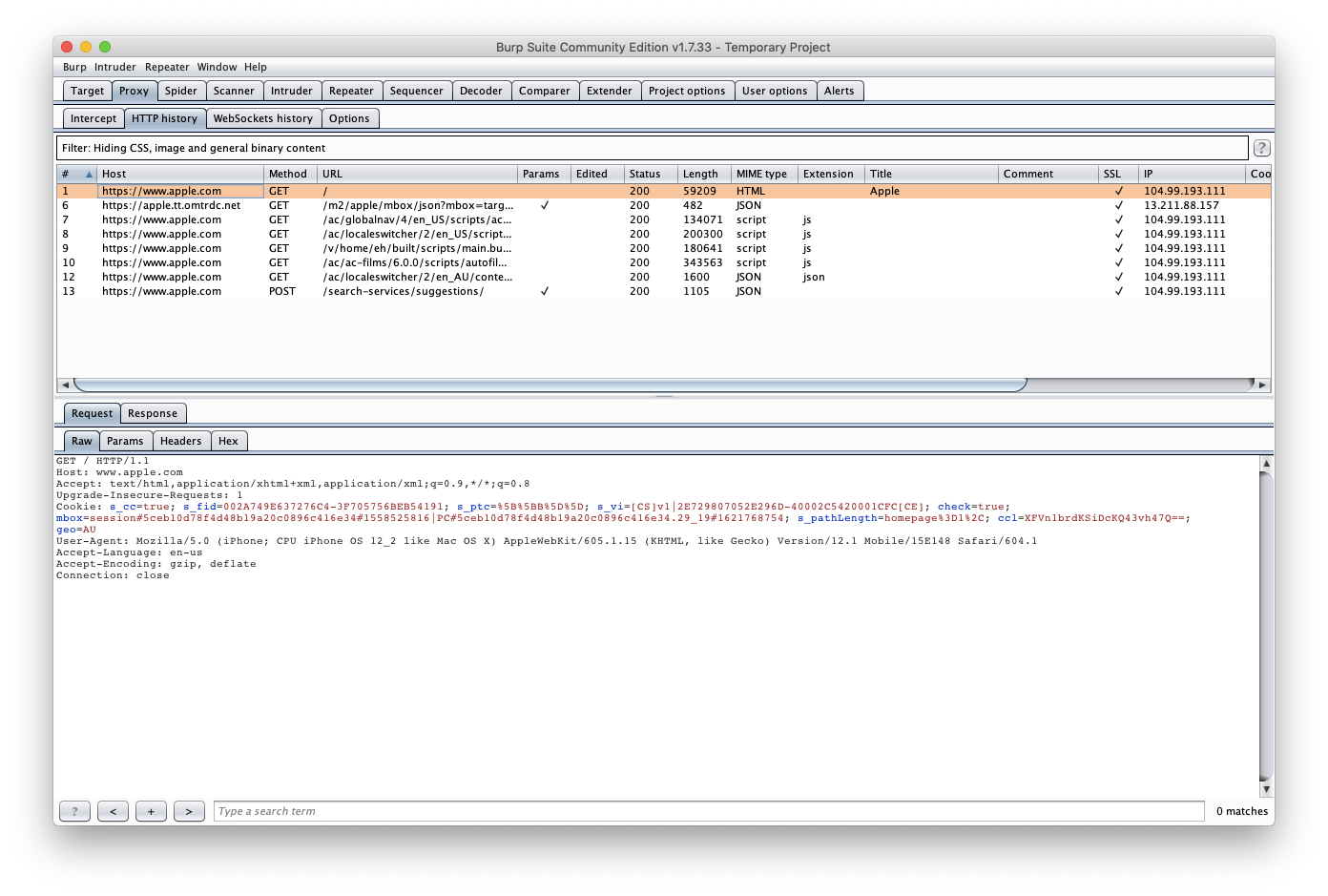
When dealing with the safety of a gadget or program, it is crucial to employ the method of analyzing network traffic. An HTTP sniffer program is needed for this purpose. PortSwigger’s Burp Suite satisfies this criterion. For this iOS hacking and security tool to function correctly while testing online applications, you must set the Burp Proxy listener to accept connections from any network device.
Major Features:
- A reliable traffic analyzer for networks.
- Automation with intelligence for economizing your time.
- Created specifically to assess modern web applications.
iSpy
You may not need tools besides BishopFox’s iSpy iPhone reverse engineering program to analyze iOS applications dynamically. Class dumps, instance tracking, evading jailbreak detection, and evading SSL certificate pinning are just some of the features accessible through its straightforward online interface.
Major Features:
- Outstanding analysis of the application’s dynamic properties.
- Group work notes, evading SSL certificate pinning, etc.
Hopper App

Disassemble, decompile, and debug iOS apps with the help of Hopper Dissembler, a reverse engineering tool. In the strictest sense, this is not an iPhone hacking tool. You can use this tool to disassemble and reconstruct software. After the application has been launched on macOS or Linux, the cracked binary must be specified as the destination and the process allowed to proceed. Reverse engineering iOS apps and collecting bug bounties is a breeze using Hopper.
Major Features:
- Software for breaking into iOS devices.
- Ideal for code-forking and refactoring projects.
Cycript
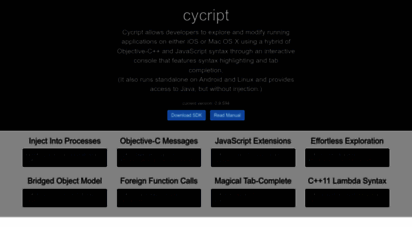
When analyzing the dynamic behavior of apps on the iPhone, iPad, and other iDevices, Cycript is the best tool available. It’s an interpreted version of JavaScript that can also solve Objective-C code. Cycript helps analyze the performance of an iOS app during its runtime, which is a common task for anyone dealing with iOS security or app analysis. With it installed on a jailbroken device, developers can insert breakpoints in sensitive areas of iOS apps without triggering the app’s security checks.
Major Features:
- Perfect for delving into iOS app performance.
- Jailbroken gadgets have the option to receive breakpoints.
Paraben DS
Forensic investigators often use the well-known Paraben Device Seizure to examine mobile devices. Simply download and run the program on your computer, then connect your iPhone or iPod touch to it. Data capture, logical and physical imaging, app data parsing, password bypassing, virus identification, and data carving are only a few of the critical features of this program.
Major Features:
- Ways around passwords.
- Finding malware, collecting information, and segmenting data.
Frida
Injecting the JavaScript V8 engine into the process runtime, Frida is a popular iPhone hacking app in 2022. It can function in both the With Jailbreak and Without Jailbreak states. Frida’s Jailbreak simplifies controlling software and system services.
Major Features:
- The jailbreak mode on an iOS device grants access to all system services and apps.
Firecat
Firecat is an iPhone hacking and network penetration tool that you may use to establish reverse TCP tunnels from within an infected network. This iPhone hacking tool requires an external host to connect to any port after a tunnel has been built, regardless of how restrictive the target network’s firewall or NAT gateway is.
Major Features:
- Makes a TCP backdoor connection from the host to the firewall.
- Supports hosts behind NAT barriers.
Highster Mobile

You might refer to it as an iPhone surveillance program instead of an iPhone hacking app. Invisibly and secretly monitor a mobile device with Highster Mobile. This app allows you to control a device from a distance, keep tabs on what’s happening in your computer’s dashboard, and uninstall itself whenever you like.
Major Features:
- There is no need to jailbreak your iOS device for use.
- It’s possible to monitor incoming and outgoing calls, send and receive text messages, and access your social media accounts, files, and media.
I think you found this compilation of the best Hack Apps for iOS and security tools useful. What methods and equipment are available for testing iOS security? Contribute your ideas and join the discussion.
What is Cydia? Why should I know about it?
Simply put, Cydia is a different App Store for iOS devices, including the iPhone, iPad, and iPod Touch. Numerous Hack Apps for iOS are made available that Apple has chosen not to include in the App Store because they violate the company’s policies.
The option to install Cydia is typically provided if a phone is jailbroken, a process comparable to rooting an Android device. Installer.app/AppTap can be used to set it up on its own. Many of the applications and resources mentioned above can be downloaded and installed with the help of Cydia. Consequently, a jailbroken iDevice must operate many iPhone hacking applications and reverse engineering tools.
You can also suggest these hacking movies to your pals if they’re looking for some nerdy entertainment.
FAQs
Can an iPhone be hacked?
The iPhone, like any other electronic device, might be compromised. The most effective approach to always having the most recent version of iOS on your smartphone.
Which is the best hacking app for iPhone?
Compared to Android, there is a shortage of morally sound hacking tools for the iPhone. Tools like Burp, Cycript, Hopper, etc., can be used as a jumping-off point.
What is Jailbreaking?
To gain root access and install non-Apple software on an iOS or iPadOS device, a process known as “jailbreaking” is used.




